Recent Articles
Guide: How to route Docker logs correctly in New Relic
Created: - 6 minutes read - 1260 words
Streamlining Container Log Management for Clarity and Control
Hello, New Relic aficionados! Picture this: you’re at a bustling local user group meetup, exchanging ideas and sharing tech stories. Amidst the animated discussions and clinking coffee cups, a fellow developer—let’s call him Alex—shares a frustrating puzzle. Alex’s Docker Compose applications are acting like rebellious teenagers, sending their logs to the New Relic Host UI instead of their designated New Relic Container UI.
read more
A Deep Dive into Zero-Day Vulnerability Alerts with New Relic APM
Created: - 7 minutes read - 1352 words
Empowering Developers with Real-Time Security Insights and Proactive Vulnerability Management
Amidst the ever-evolving landscape of cybersecurity, the recent revelation of a zero-day vulnerability in Fortinet’s FortiOS serves as a stark reminder of the constant cat-and-mouse game between defenders and attackers.
Staying ahead of potential security threats isn’t just a best practice; it’s a necessity. For developers, the challenge lies not only in identifying vulnerabilities but in doing so proactively, especially when it comes to zero-day exploits.
read more
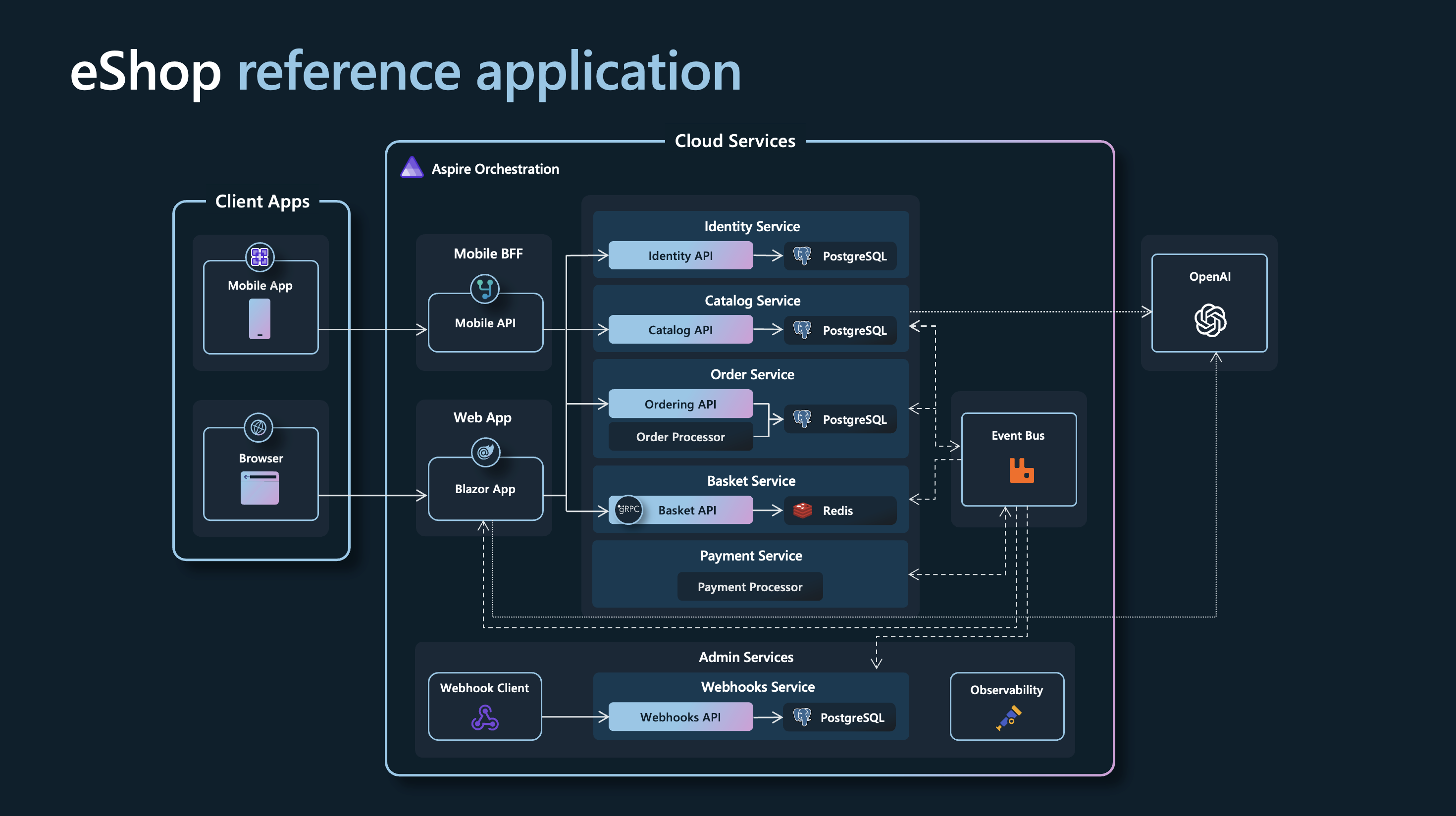
Using .NET Aspire eShop application to collect all the telemetry
Created: - 5 minutes read - 1017 words
Read this guide on how to collect all the telemetry from the .NET Aspire eShop application into an OpenTelemetry backend such as New Relic
.NET Aspire is the new kid on the block when it comes to an opinionated, cloud ready stack for building observable, production ready, distributed applications. Having a built-in dashboard for the monitoring data is nice during development. But how do you configure OpenTelemetry correctly to send into an observability backend?
read more
How to monitor Microsoft 365: Observing AD FS
Created: - 7 minutes read - 1484 words
A practical guide to Active Directory Federation Services for a resilient Microsoft 365 ecosystem
In our previous blog on how to monitor Microsoft 365 (M365), we delved into service overviews and the critical importance of synthetic user login monitoring. In this blog, we set our sights on a core component that forms the backbone of secure identity and access management: Active Directory Federation Services (AD FS).
As organizations increasingly migrate their operations to the cloud, ensuring the robustness of identity and authentication mechanisms becomes paramount.
read more
How to use CodeStream—and shift left your observability practice
Created: - 8 minutes read - 1577 words
Your adventure in the world of observability, performance optimization, and security begins here.
In the fast-paced world of software development, the quest for smoother, more efficient applications feels like a never-ending adventure. But in this adventure, it’s not about slaying dragons or uncovering hidden treasures; it’s about ensuring your code performs seamlessly and your users are happy.
As a developer, I’ve faced the challenges of reactive observability, where we typically identify and resolve issues only after they’ve disrupted our applications.
read more